5 Best Hardware Solutions for iPhone Hacking In today’s tech-driven world, iPhones hold a dominant position, often regarded as a gold standard for smartphone security. However, despite Apple’s robust security measures, hacking into an iPhone is not an insurmountable challenge. Hackers and forensic investigators often employ hardware solutions to access iPhone data without relying solely on software methods. This article explores the top 5 hardware solutions designed for iPhone hacking, offering insights into their functionalities and ethical considerations.
Hardware Solutions Overview
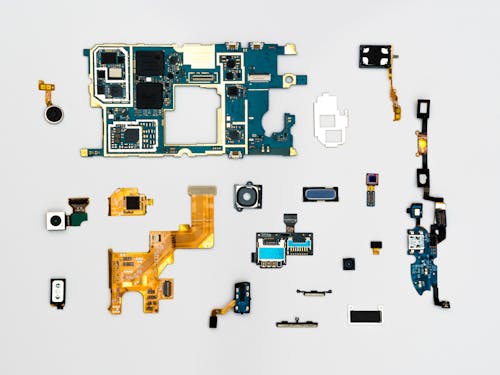
Before delving into specific hardware solutions, it’s crucial to grasp the concept of iPhone hardware hacking. This approach involves manipulating the physical components of the iPhone, bypassing security features to gain access to sensitive data stored within the device. Unlike software-based methods, hardware solutions can directly interact with the iPhone’s hardware components, making them potent tools for accessing data.
The Top 5 Hardware Solutions for iPhone Hacking
Solution 1: NAND Mirroring
NAND mirroring involves creating a copy of the iPhone’s memory (NAND chip) and repeatedly writing it back to restore the original state after unsuccessful passcode attempts. Although effective, this method requires technical expertise and specialized equipment, making it less accessible to the average user.
Solution 2: IP Box
The IP Box is a hardware tool that exploits vulnerabilities in older iPhone models to brute-force passcodes. It automates the entry of numerous passcode combinations until the correct one is found. However, its effectiveness is limited to specific iPhone models and iOS versions.
Solution 3: GrayKey
GrayKey is a popular forensic tool used by law enforcement agencies. It connects to an iPhone via the lightning port and employs brute-force techniques to crack passcodes. Its user-friendly interface and high success rate have made it a sought-after solution among forensic professionals.
Solution 4: Cellebrite UFED
Cellebrite UFED is another widely used forensic tool capable of extracting data from iPhones. It bypasses security measures to access information, allowing forensic investigators to retrieve valuable data for legal purposes. However, its usage is strictly regulated and requires adherence to legal protocols.
Solution 5: Minicomputer and DIY Solutions
For tech-savvy individuals, building a minicomputer or DIY hardware solution offers a customizable approach to iPhone hacking. These solutions involve assembling hardware components and employing specialized software to exploit vulnerabilities and gain access to iPhone data.
Pros and Cons of Each Hardware Solution
Each hardware solution comes with its own set of advantages and drawbacks. While some provide high success rates, they might require specialized knowledge or have legal implications. Understanding these trade-offs is crucial before utilizing any hardware solution for iPhone hacking.
Legal and Ethical Implications of iPhone Hacking
The use of hardware solutions for iPhone hacking raises significant legal and ethical concerns. Unauthorized access to someone’s iPhone without consent violates privacy laws and ethical boundaries. It’s imperative to understand the legal ramifications and ethical considerations before employing any hacking method.
Security Measures to Protect Against Hardware Hacking
To safeguard against potential hardware hacking attempts, iPhone users can implement various security measures. These include regular software updates, utilizing complex passcodes, enabling two-factor authentication, and avoiding suspicious links or downloads.
Conclusion
In conclusion, the realm of hardware solutions for iPhone hacking presents both opportunities and challenges. Understanding the available methods, their implications, and the ethical considerations surrounding their usage is essential. It’s crucial to balance the pursuit of information with respect for privacy and legal boundaries.
FAQs
- Can these hardware solutions work on all iPhone models?
- Are hardware solutions legal to use for personal reasons?
- How can individuals protect their iPhones from hardware hacking attempts?
- Are there any free hardware solutions available for iPhone hacking?
- What steps should one take if they suspect their iPhone has been hacked using hardware methods?
If you require any hacking an iPhone or protect your device kindly hire us here for a reliable and wonderful service here: https://hireprohackers.com/


Hello, can i get a hardware for an iphone?
The efficiency of this JAMES is next level. To juggle walk throughs of various angles on the topic delivered to-camera, differnet content per topic from various folks underneath the umbrella of the track list of the larger big band concert itself is engaging and refined. To make a dense access like this so digestible is really something. Awesome work [email protected]
I need help I feel like my husband is up to no good and I don’t know much about all these digital things ask I know it’s I looked at his location the night before last and it told me left work at 10:15 pm and was touching around till 11:20 then wouldn’t you know he walked in the door! Yes, I was made with an attitude because he doesn’t drive but when I said something he said I was crazy liked at the app and said look you don’t know what you’re taking about it said (this time) that he like work at 11:06 please help.
Then sir Franko Mathew for a professional service i was able to use the software and it work perfectly. kudos to [email protected]
I offer mutually beneficial cooperation https://ztd.bardou.online/adm
Cool website. There is a suggestion https://ztd.bardou.online/adm
I really liked your site. Do you mind https://ztd.bardou.online/adm
Here’s what I can offer for the near future https://ztd.bardou.online/adm
Content for your website https://ztd.bardou.online/adm